The World Wide Web is a great place where you can visit and learn about just anything. The problem is that sometimes you can end up facing security threats of all levels you can possibly imagine. With the security concerns always coming up, many people would want to take measures to keep their systems safe from attacks. Before all that you have to know about the computer security threats that you will be facing.
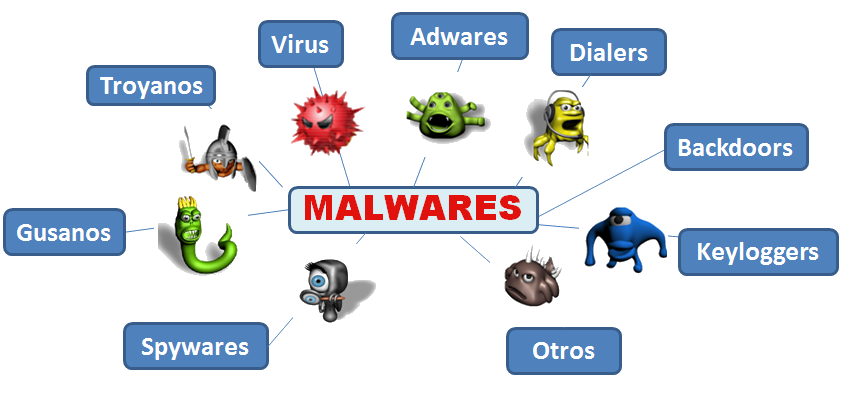
Malware
The word malware is the short for malicious software. This is basically something you would not want around your system. It does do a lot of harm by being intelligent enough to intrude the system and collect information without you knowing about it. The malware is also seen as a broad term for computer viruses, Trojan horses, spyware and malicious rootkits.
Computer virus
This is a small piece of software that spreads from one infected computer to another one. The work of the virus mostly is to corrupt, delete data, steal or even erasing your hard drive. Some people have often woken up the following day to find their systems completely erased without any alarm. Viruses mostly use emails as a way to spread itself to other computers.
Rogue security software
This often comes as a pop up window that will be advertising a security update alert. Most people would think it is legitimate and would end up clicking on it. Such sites can be quite convincing that they have detected a malware or virus on your system. Whenever you install the software, that would be the beginning of your system troubles. They will often snoop and send information to its creator.
Trojan horse
The Trojan horse comes about when you download a software thinking that you are getting a legitimate application, but it is all malicious. Once the software is installed, the Trojan horse can do a lot of stuff such as recording your passwords, logging keystrokes or even hijack the webcam to watch and record your every move.
Botnet
This is where a hacker compromises a group of computers connected to the internet. The hacker can use a computer virus or Trojan horse to make the network. He will be using the network to do all sorts of malicious stuffs such as sending spyware, extracting information from systems among many other things.





Leave a Reply